July 2025 marked a milestone for the U.S. gaming industry: gross gaming revenue hit a record $6.21 billion, fueled by strong growth in both land-based and online sectors. This surge signals not just a summer rebound,
Continue ReadingCategory: Data Protection
Protect Your Business with Strong Cybersecurity
Cybersecurity is more important than ever for businesses of all sizes. Cyber threats are constantly evolving, and protecting our sensitive data has become a critical task. Hackers are looking for any opportunity to exploit weaknesses in
Continue ReadingProtecting Your Data with Encryption Explained Simply
Protecting our data is more important than ever. With hackers constantly seeking ways to steal information, we must be vigilant. One effective way to keep data safe is through encryption. Encryption transforms our data into a
Continue ReadingMaintaining Security in the Cloud: Top Strategies for Protecting Your Data and Applications
In 2024, cloud adoption has become the norm for businesses of all sizes, seeking scalability, flexibility, and cost savings. As organizations transition their systems, applications, and data to the cloud, ensuring the security and privacy of
Continue ReadingBest Practices for Securing Your Business’s Digital Assets
As the world becomes increasingly digital, protecting our business's digital assets is more crucial than ever. Digital assets include everything from customer information and financial data to business plans and intellectual property. These assets hold immense
Continue ReadingOptimizing Your Business’s Cybersecurity Framework: A Comprehensive Guide
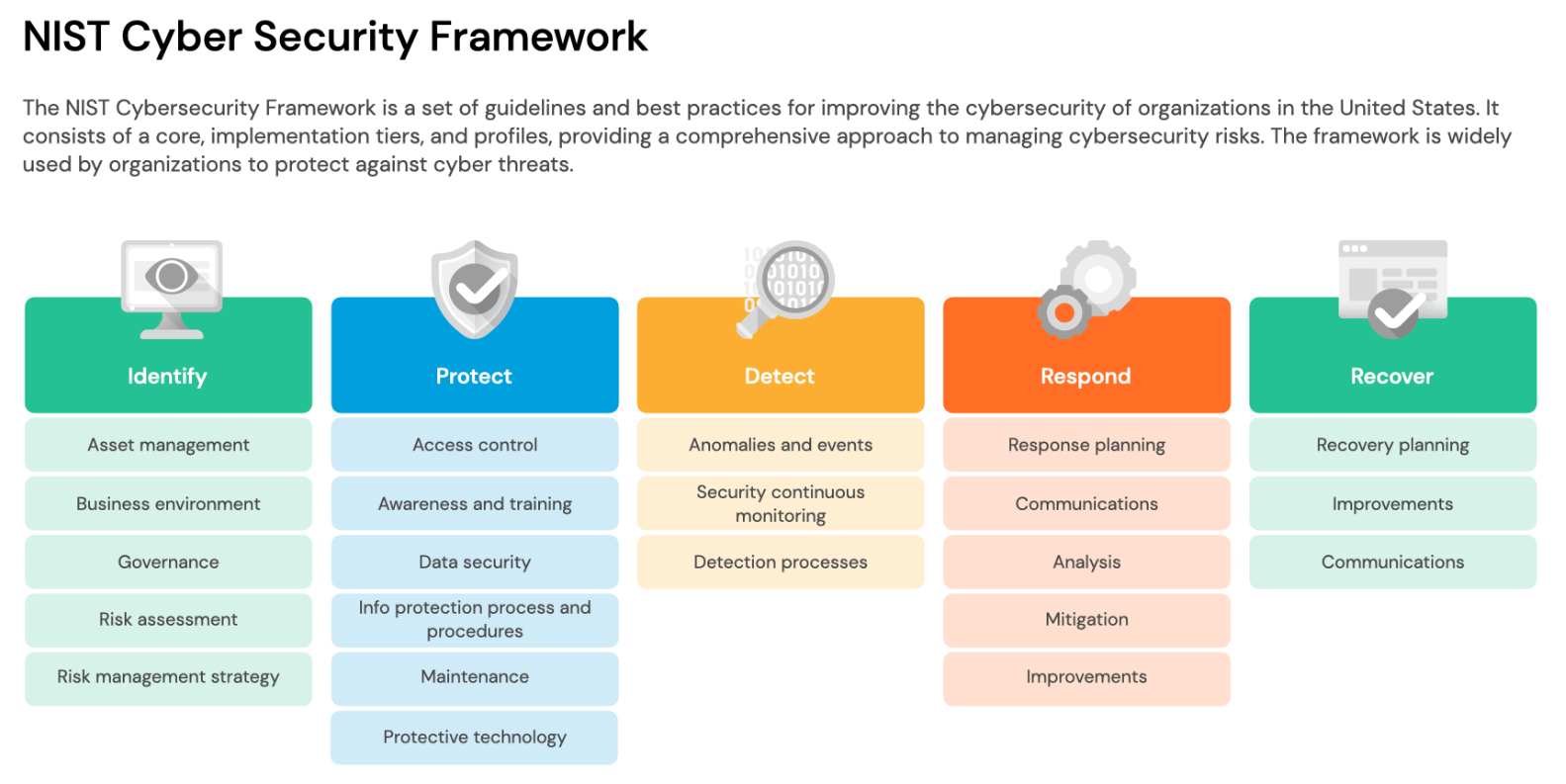
Cybersecurity is not just a technicality but a foundational component of any successful business operation. As we continue to integrate more sophisticated technologies into our daily workflows, the complexity of our cyber environments increases. This escalation
Continue ReadingEmbracing Zero Trust Security: Guiding Your Organization Toward a More Secure Future
As cyber threats become more sophisticated and prevalent, organizations must adapt their cybersecurity strategies to keep pace with the ever-changing digital landscape. Traditional security approaches, which often rely on perimeter defenses and a "trust but verify"
Continue Reading